How to Configure Azure Key Vault?
Azure Overview and Key Vault configuration
Microsoft Azure Key Vault (AKV) helps a lot from HSM hardware misery and is a great feature in the cloud to store, safeguards and manages digital keys for strong authentication without taking headache to manage with Hardware Security Module (HSM). Microsoft provides Azure Key Vault as a simple interface by using which we can access the HSM device in a secure way to storing information in a database. After following the under listed instruction, how to configure azure key vault will be real easy.
The data doesn’t simply stay in a file on server. This information is stored in hardware device and the device provide many features like auditing, encryption, etc. The excessive object in AKV is that even Microsoft can’t see or extract your keys. Microsoft does takes care of patching, provisioning, and other infrastructure related issues. We can store Subscription Keys, Database Connection strings, License Keys, PFX files and manage SSL certificates using AKV and many other type of keys could be stored and managed easily by using AKV.
Requirements & Steps to configure Azure Key Vault:
-
Subscription
Azure subscription is the first step to access anything under provided services in Azure portal. A valid Windows Azure subscription grants you access to Windows Azure services and to the Windows Azure Platform Management Portal. The subscription holder manages all serveries and activates through the Windows Azure Platform Management Portal. Services which are included are most likely Windows Azure, SQL Azure, Storage etc…
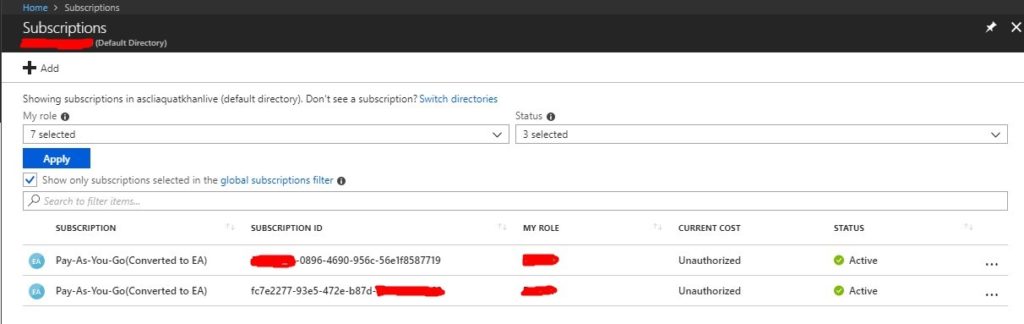
The best practice is that to create separate subscription for Dev, Test and Production environment. Subscriptions allow for a single Azure instance to separate these costs, and bill to different teams. It can help in multiple ways that you can monitor billing and usage for each of this environment separately and to ensure security that can have different co-admin for each of this Subscription. Below mentioned is a screenshot to just give an idea about subscriptions:
-
Azure Active directory
Azure Active Directory provides on-premises and cloud identity management solution along with capabilities to secure application access control, federation, information protection, standard protocols support etc… into a single solution. Azure AD also offers a broad and standards-based platform that allows developers to deliver access control to their applications, based on centralized policy and rules. There is different type of Microsoft Azure AD editions which are much flexible and can be deployed according to the requirement:
- Basic
- Premium P1
- Premium P2
- Key Vault creation
Step 1 Key vault:
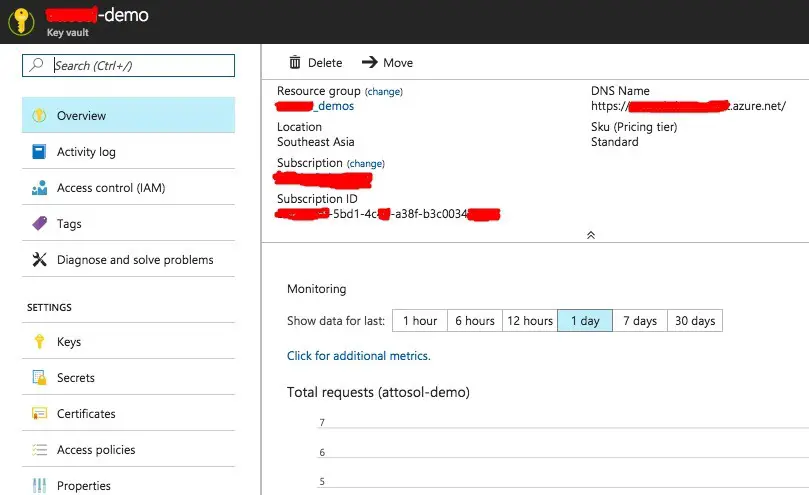
- Login Azure Portal> Click New > Key Vault > Create
- You can give name as per desire and select subscription.
- Select resource group and Location as per requirement and click on create button.
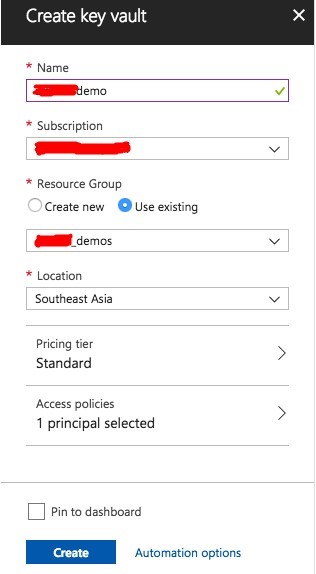 This process takes less than a minute usually. Note down the URL of your key vault (DNS Name) as it is required later.
This process takes less than a minute usually. Note down the URL of your key vault (DNS Name) as it is required later.
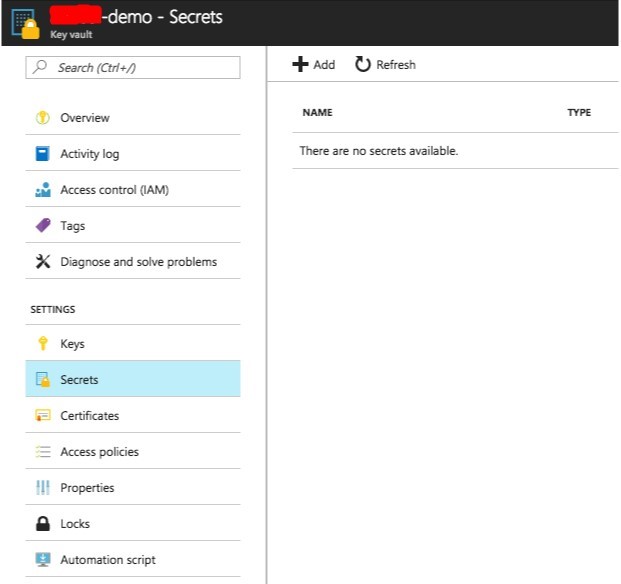
Click on Secrets in the blade under newly created key vault. Click on Add button on the top right to add secret.
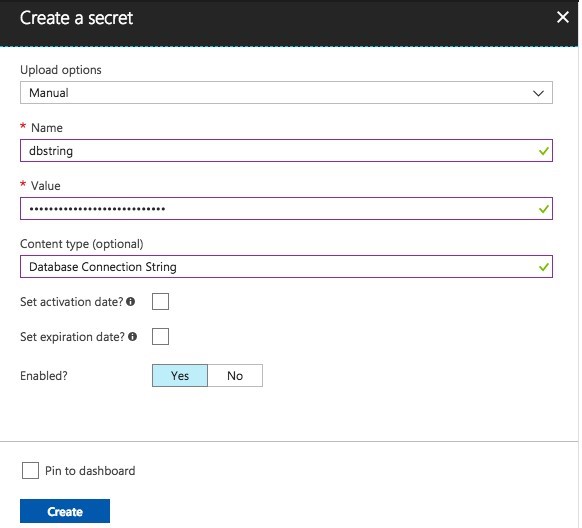
 Fill the required secret details and click on create button:
Fill the required secret details and click on create button:
 Step 3 Register an Application and create keys:
Step 3 Register an Application and create keys:
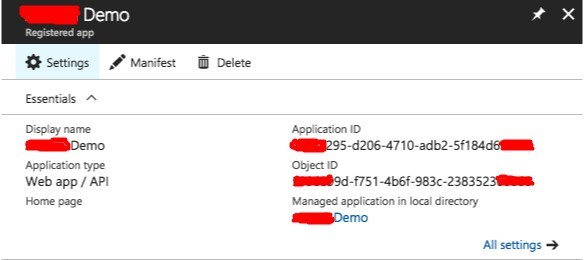
- Azure Portal > Azure Active Directory > App Registrations > New
- After filling information, click on create button at bottom.
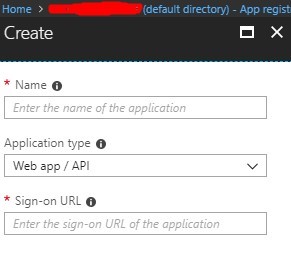 Note down the details. Remember, client id is same as Application ID.
Note down the details. Remember, client id is same as Application ID.
Go to app registration and click on settings then keys to create a key. You can use the server’s host name as the key description. If this server is compromised, you can revoke the access to AKV by simply deleting this key.
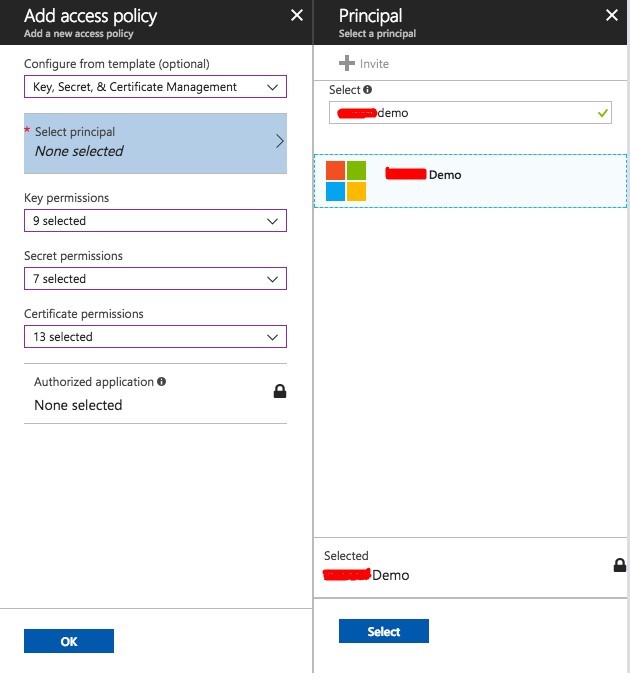
Step 4: Give Permission to App:
- Azure Portal Dashboard
- Search Key Vault in search bar and open it
- Select the recently created key vault
- Access Policies > Add New > Select Principal
- Key vault required configurations after finishing above steps: Just provide these four values to your developer or someone who is configuring the application and you are good to go.
- Endpoint
- Application ID
- Client Secret
- Key Vault URL
For official documentation please follow configure azure key vault